This new year brings a new challenge for us SCCM administrator. The Speculation Control vulnerability (aka Spectre and Meltdown) affects many modern processors and operating systems and is considered critical to patch. The first challenge is to monitor who is vulnerable in your organization. The second one is to understand this beast and to remediates it. The important thing to know here is that a machine needs more than only a Windows OS patch to be compliant. There’s also a hardware level firmware updates to apply. This blog post will focus on the monitoring part to be able to show your management if you’re compliant or not.
We also included a free report to download in order to track your Spectre and Meltdown compliance level. You can jump at the end of this post if you want to download it and skip the reading.
SCCM Spectre Meltdown Configuration Baseline Creation
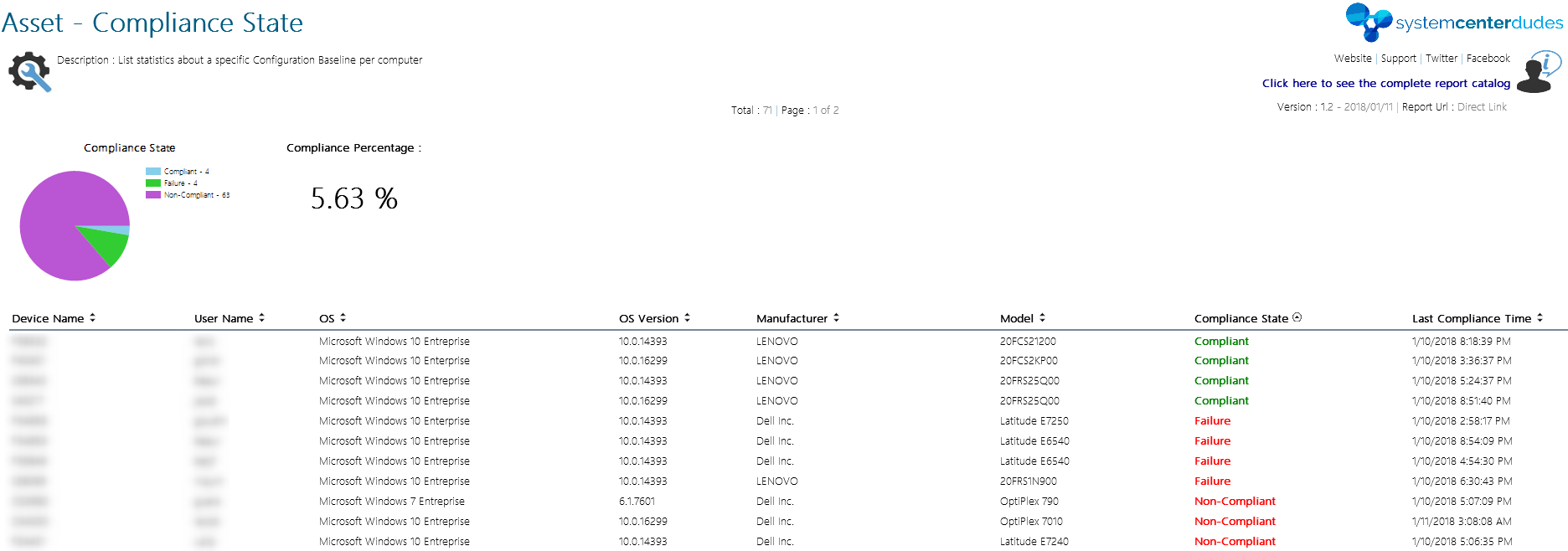
Luckily for us, Microsoft PFEs, Ken Wygant make the dirty work for us and has created an incredible job in turning a detection Powershell script into a ready-to-import SCCM Configuration Item and Baseline. They did a pretty good blog post explaining their work and we’ll use their CAB file in order to show you the step-by-step process in order to use it in your organization.
The first step is to download the CAB file.- [Edit 01/15] Microsoft has released a new Configuration Baseline available on Technet Gallery. The new cab file will create only 2 CIs instead of 8 but the blog post is still relevant.
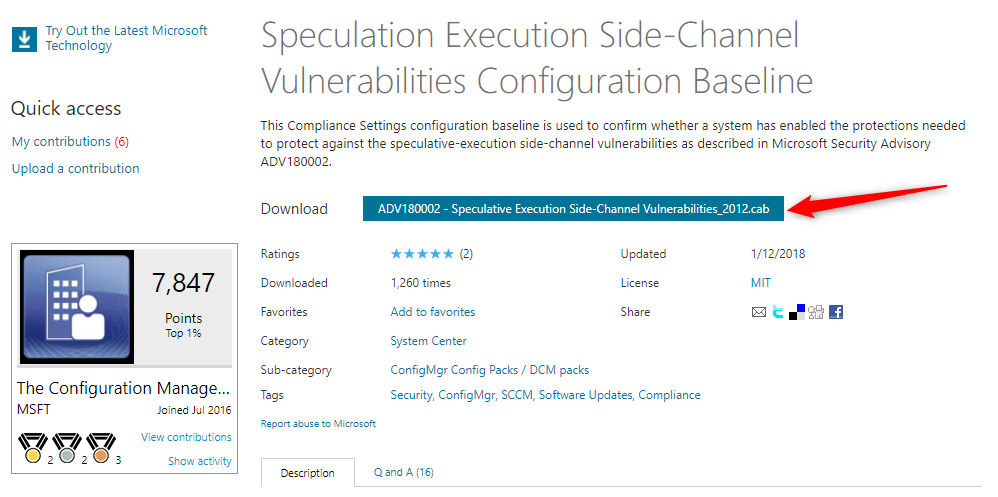
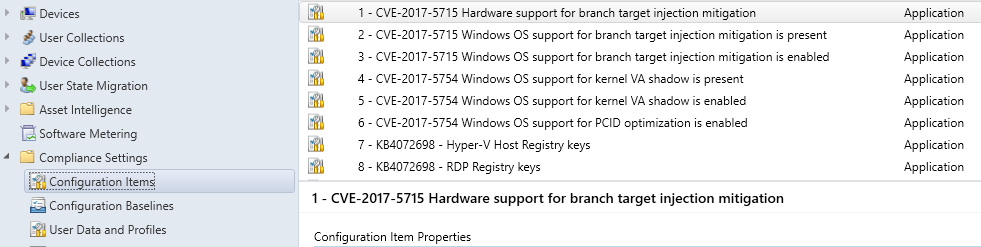
- In the SCCM Console, go to Assets and Compliance / Compliance Settings / Configuration Items
- Right-Click Import Configuration Data
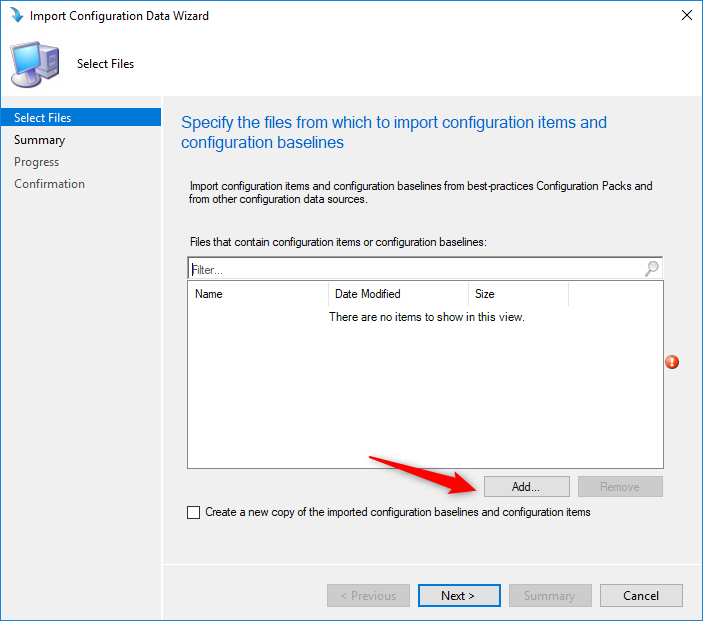
- In the Import Configuration Data Wizard, click on Add
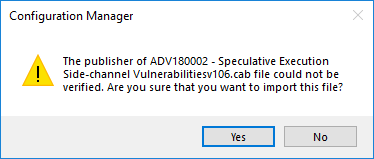
- On the security warning, click Yes
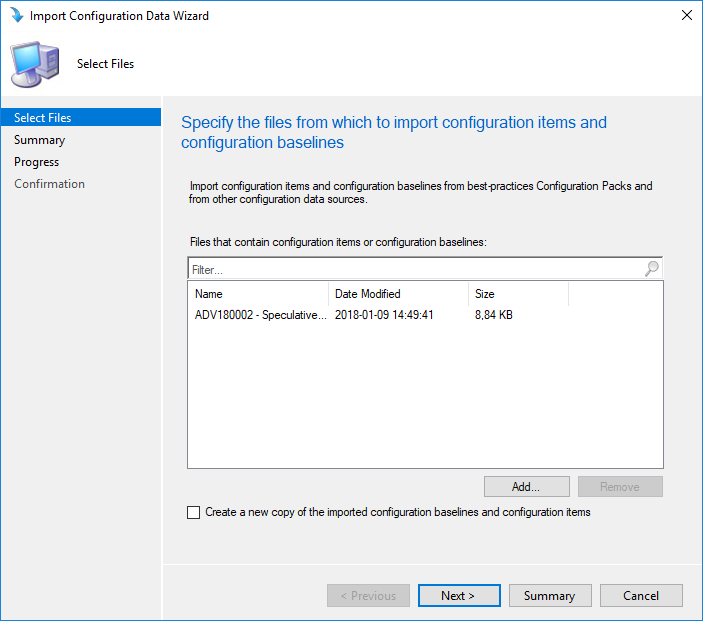
- The Configuration Baseline appears in the file window, click Next
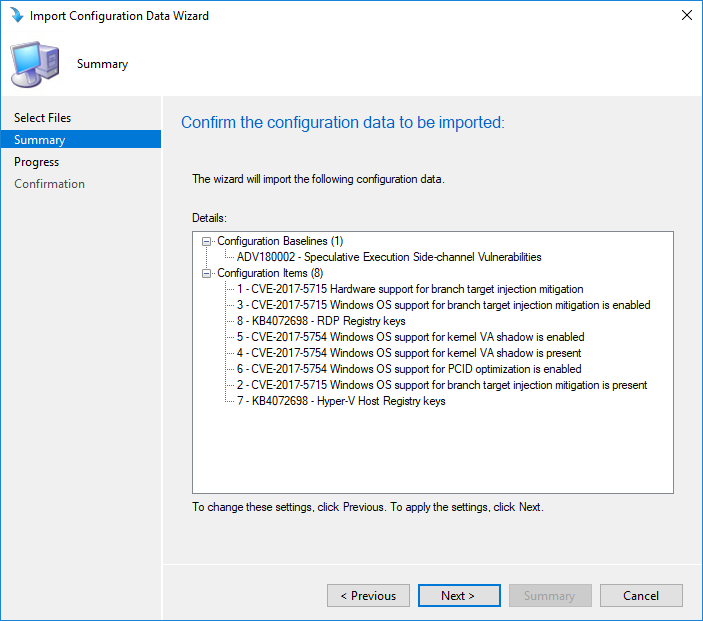
- Review the Summary, click Next and complete the wizard
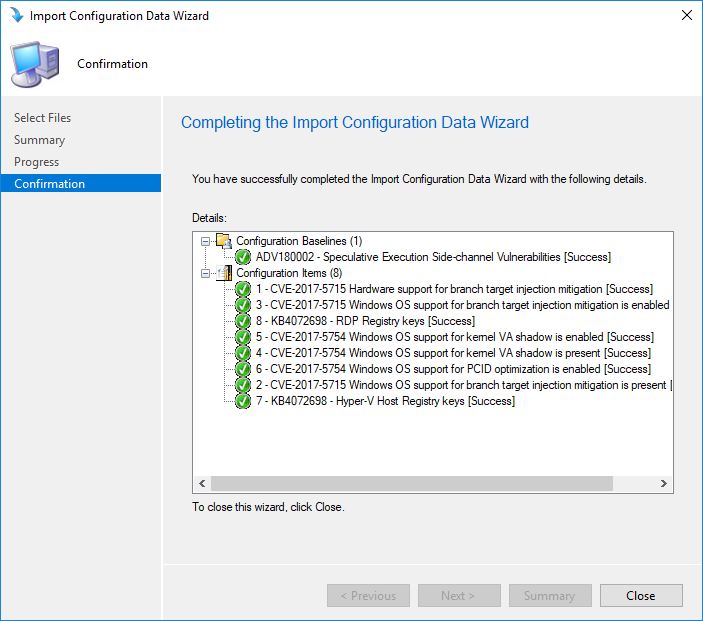
- Back in the Configuration Item pane, the 8 CI are created
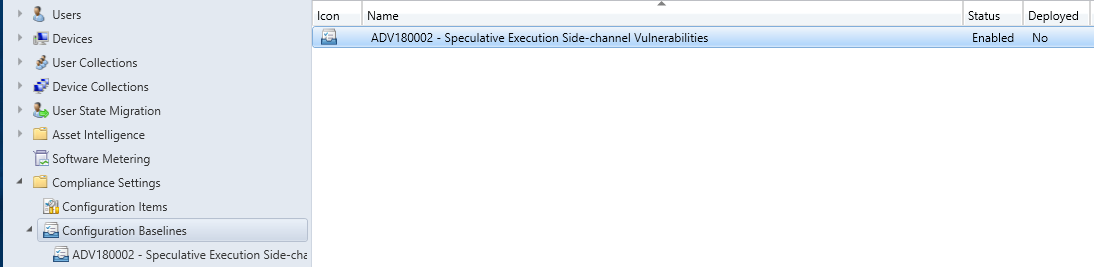
- In the Configuration Baseline pane, the Baseline is created. This baseline contains the 8 CI and is ready to be deployed
SCCM Spectre Meltdown Configuration Baseline Deployment
We will now deploy the Configuration Baseline to a test collection in order to validate it.
- In the SCCM Console, go to Assets and Compliance / Compliance Settings / Configuration Baseline
- Right-Click the ADV180002 – Speculative Execution Side-channel Vulnerabilities Baseline and select Deploy
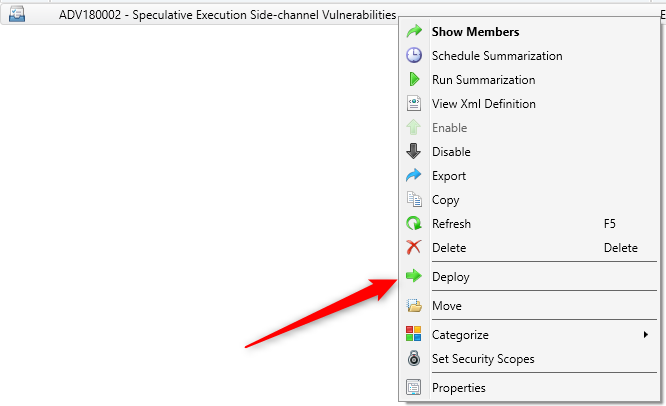
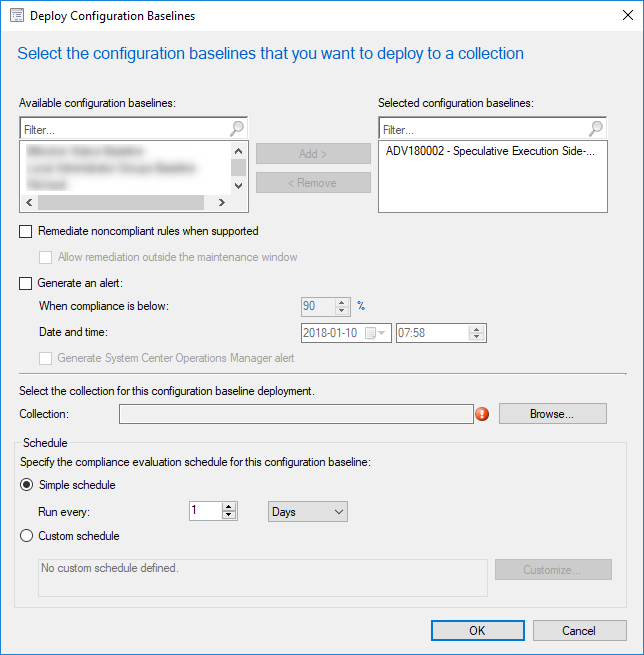
- Select the collection which contains your test machines by clicking Browse, select your compliance evaluation schedule and click Ok
SCCM Spectre Meltdown Workstation Validation
On a machine that receives the configuration baseline :
- In Control Panel, open the Configuration Manager Properties application
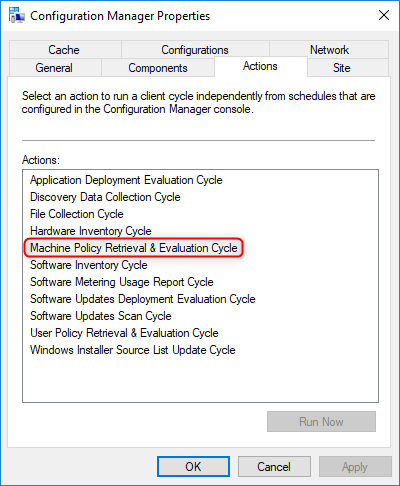
- Initiate a Machine Policy Retrieval & Evaluation Cycle to receive the baseline
- In the Configuration tab, click Refresh until the baseline appears
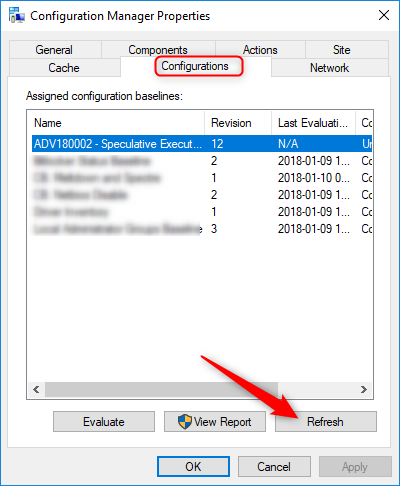
- Once the baseline is available, select the ADV18002 Baseline, click Evaluate and wait a couple of minutes
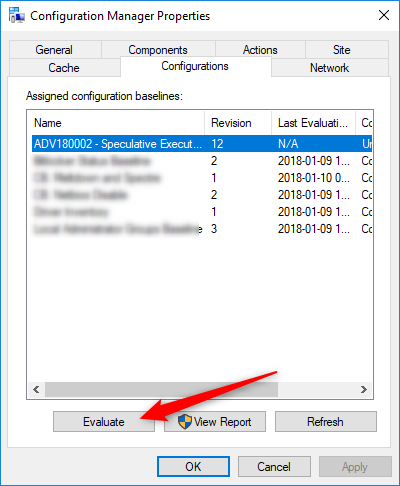
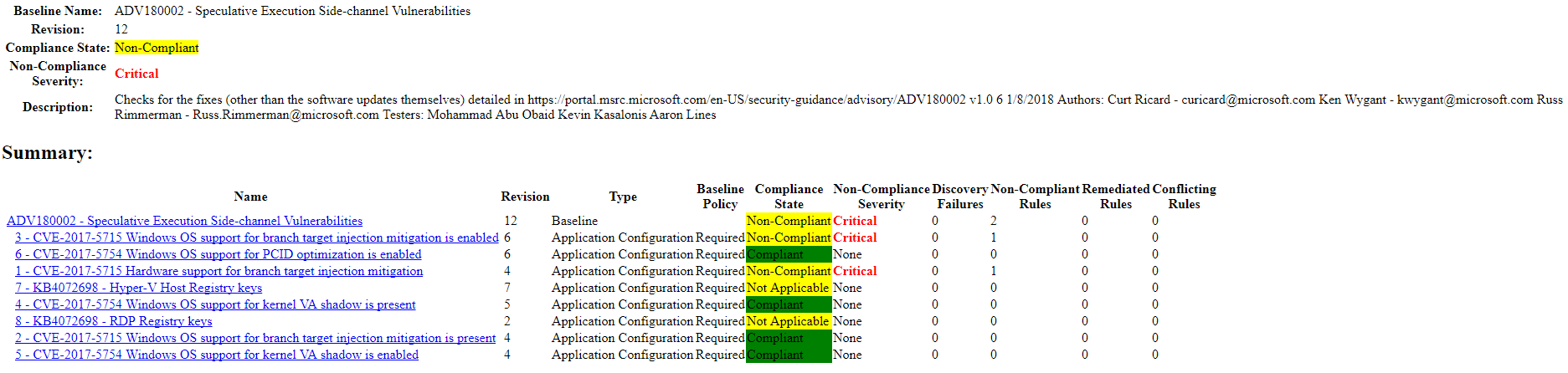
- Once the Last Evaluation Date get populated, click View Report
- Your browser will open the report showing the compliance state of this machine. In our screenshot, my machine has a compliant state in 4 out 8 CIs. This is because I’ve applied the Windows 10 OS patches but the hardware level has not been patched
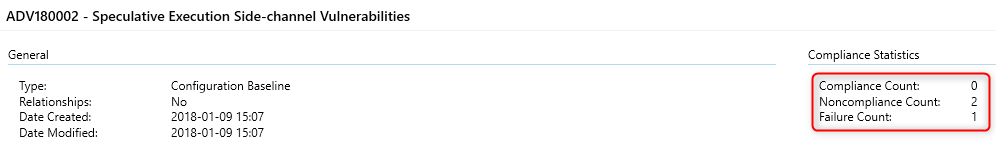
- In the SCCM console, the compliance statistics will begin to populate. This will confirm that your work has been well made.
SCCM Spectre Meltdown Configuration Baseline Report
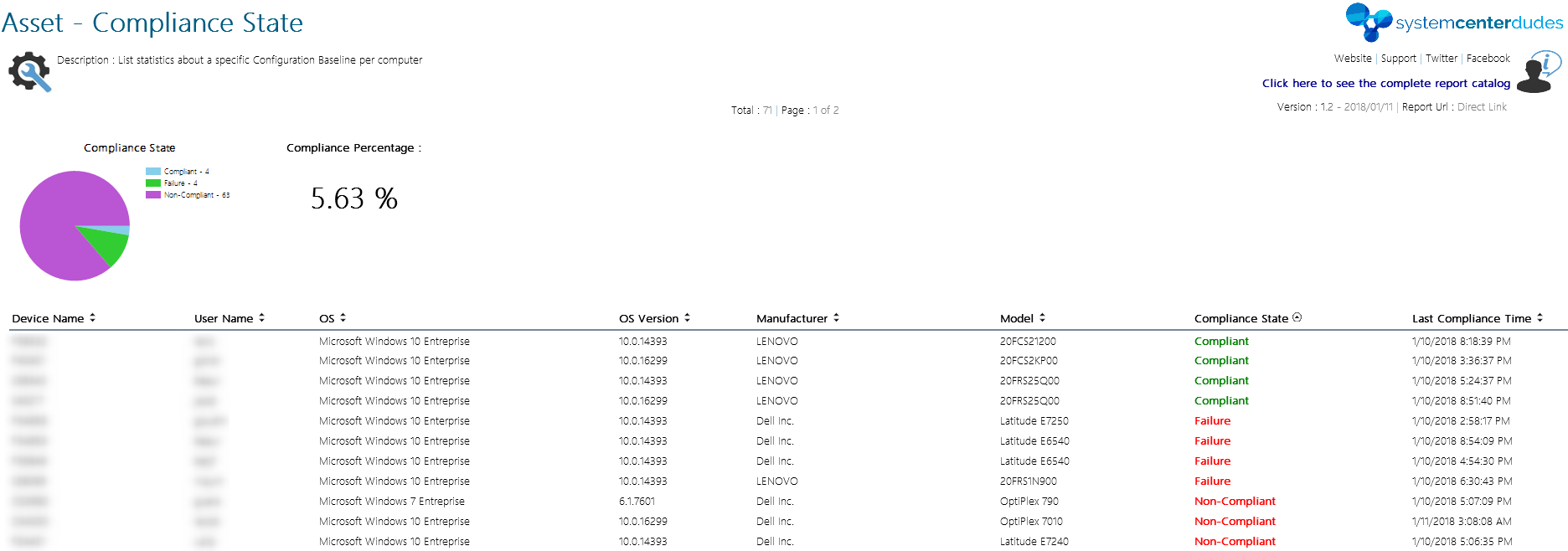
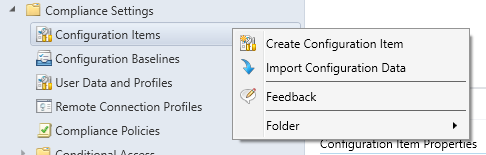
The console statistics are basic and doesn’t permit to know which machines are compliant or not. We’ve created a simple report to let you know the list of machines and their compliance state. This report will ask which Baseline to show, just select the baseline we just created in this blog post to see you Spectre / Meltdown statistics.
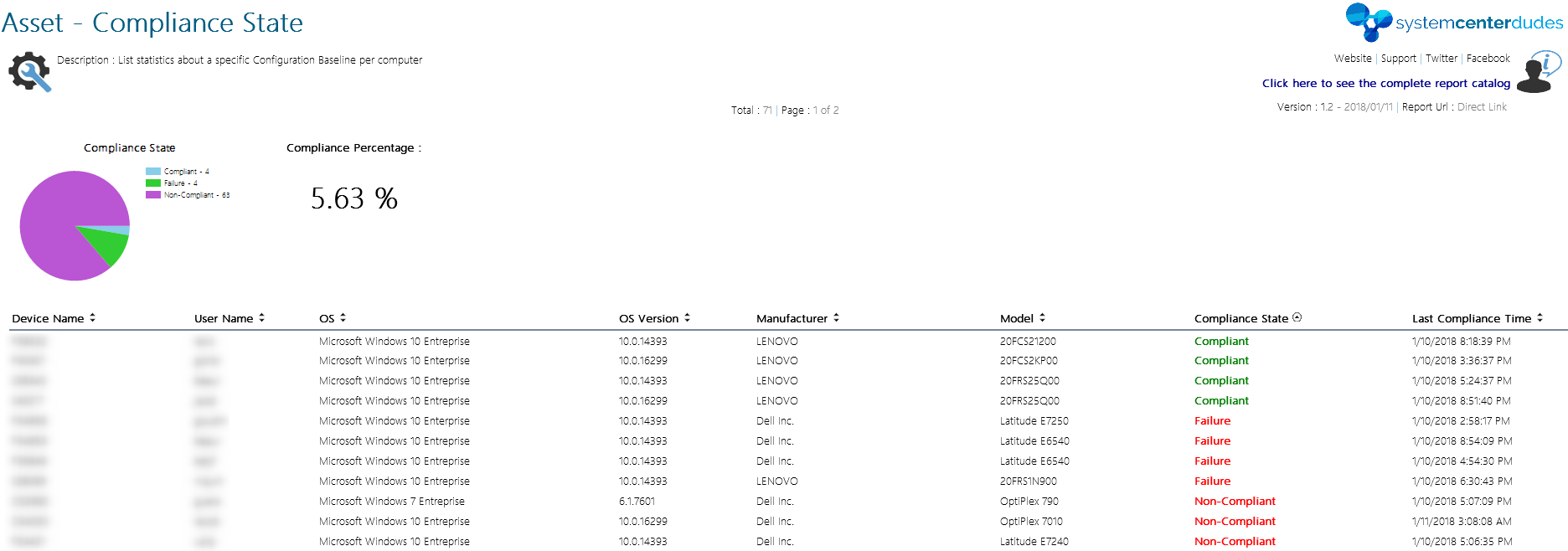
You can download this free report by visiting our product page. The Asset – Compliance State report is available in the Report / Asset Section.















Alan Yousif
05.21.2019 AT 09:03 AMNate Bishop
02.13.2019 AT 04:07 PMhashmat
02.01.2019 AT 01:50 PMdaryl
06.06.2018 AT 02:46 PMChristoph von Wittich
04.20.2018 AT 02:02 AMDavid Geiger
03.27.2018 AT 08:41 AMMichael Sweeting
02.23.2018 AT 08:44 AMBill
04.24.2018 AT 12:30 PMSushant Shriram Narlawar
01.23.2018 AT 04:24 AMmunzi
01.19.2018 AT 08:12 AMJonathan Lefebvre
01.22.2018 AT 10:23 PMIan
01.18.2018 AT 04:55 AMBenoit Lecours
01.18.2018 AT 10:39 AMMercury
01.18.2018 AT 04:06 AMMichele
01.17.2018 AT 04:26 PMBenoit Lecours
01.18.2018 AT 10:36 AMIlyaP
01.16.2018 AT 03:18 AMBenoit Lecours
01.18.2018 AT 10:32 AMRick
01.15.2018 AT 03:28 PMRick
01.15.2018 AT 03:26 PMJessie
01.13.2018 AT 03:17 PMPhilippe Fournier
01.12.2018 AT 11:35 AMBenoit Lecours
01.12.2018 AT 02:31 PMPhilippe Fournier
01.18.2018 AT 10:51 AMsachinkpshinde
01.11.2018 AT 01:27 AMBenoit Lecours
01.18.2018 AT 10:28 AMRuss Rimmerman
01.10.2018 AT 09:16 PMBenoit Lecours
01.12.2018 AT 02:32 PMBenoit Lecours
01.15.2018 AT 08:49 AMNazim
01.10.2018 AT 03:05 PM