This blog post describes how to fix SCCM Bitlocker prompt for fixed drives when integrated the MBAM features with Configuration Manager.
Introduction
Starting with Configuration Manager 1910 onwards, Bitlocker features that were available in MBAM are now fully integrated into ConfigMgr and allows you to manage the Bitlocker drive encryption (BDE) for your windows clients without requiring any additional tools.
From Configuration Manager 2002 onwards, the Bitlocker management feature is no more a pre-release feature.
The Bitlocker functionalities that exist in Configuration Manager 1910 onwards, only supports the clients that are on-prem and joined to Active Directory ONLY.
You will not be able to use the Bitlocker features for clients that are Azure Active Directory-joined, workgroup clients, or clients in untrusted domains. The clients that are not on-prem domain joined, will not be able to authenticate with the recovery service to escrow keys.
For more information on how to set up the Bitlocker and deploy the policies, please refer to the Microsoft Documentation. For deployment and configuration of Bitlocker management using Configuration Manager, please refer to the Microsoft Documentation.
I was recently working with a customer who wants to implement the Bitlocker management using Configuration Manager 2002 and helps to eliminate the need of storing the keys in AD.
Just to give some information on the SCCM infrastructure, the customer was using ConfigMgr 2002 build with eHTTP and is self-signed certs. The Cloud Management Gateway was using public cert (Digicert). There is no PKI infra at all. Clients were using token-based authentication for CMG.
SCCM Bitlocker Prompt Problem
The Bitlocker policy helps you configure the drive encryption policy for OS drive and fixed drives.
Since the customer has a mix of devices with fixed drives, the policy should contain the Bitlocker settings for both OS and fixed drive.
When you create a policy with OS drive encryption and deploy it, the BDE process is seamless, and there is no UI prompt to the user, and it just works fine.
There are many options for you to choose when a fixed drive is present, and this is where I had the problem with the end-user experience.
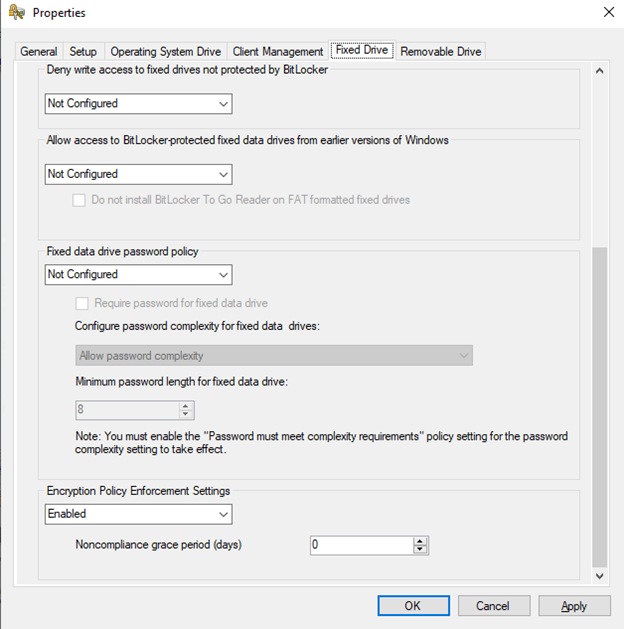
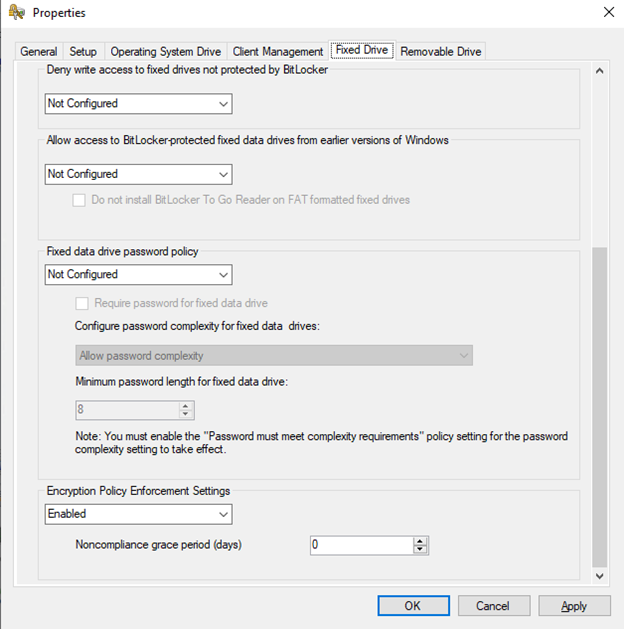
So as part of the BDE for fixed drives, I have the following settings configured.
When the policy is deployed to clients that have fixed drivers, the user started seeing the following screen:
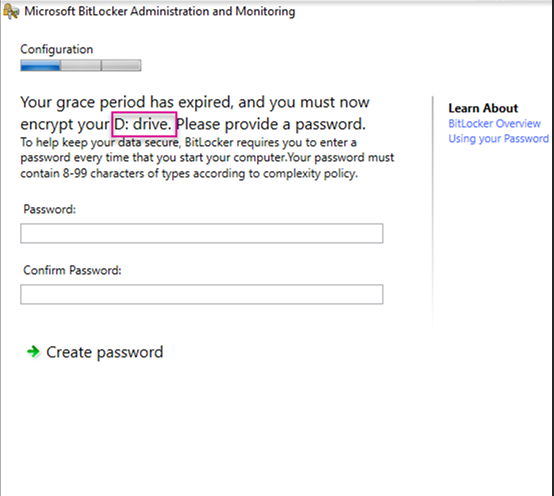
When end-users see this message, they have no idea what to do next.
How to Fix
The above UI prompt is happening due to the policy-setting we did in the Bitlocker policy in the fixed drive tab.
I took little time to read through the description of each setting configured in the fixed drive policy.
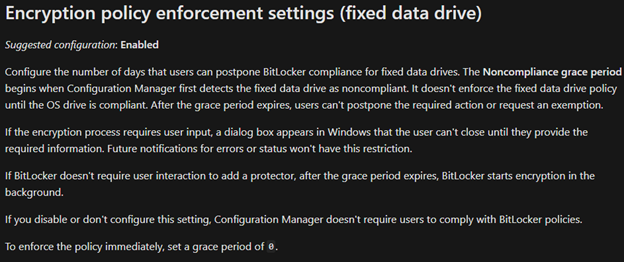
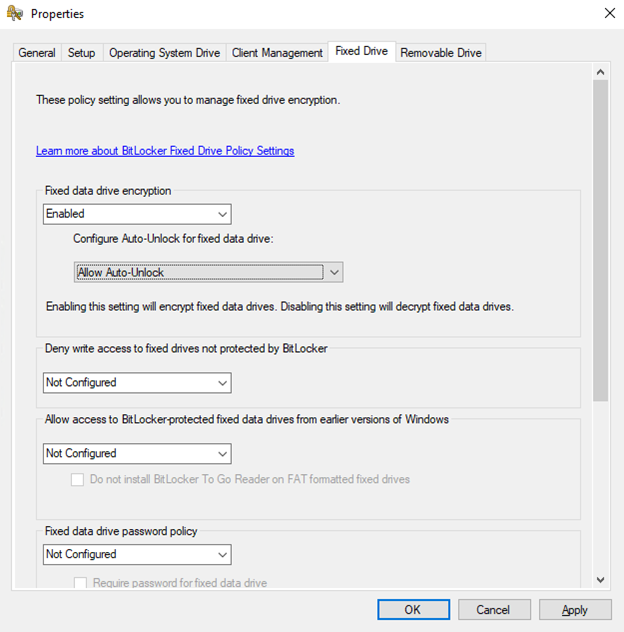
Based on the above theory, we have 2 options to disable the user input for the fixed drive encryption and make it completely seamless.
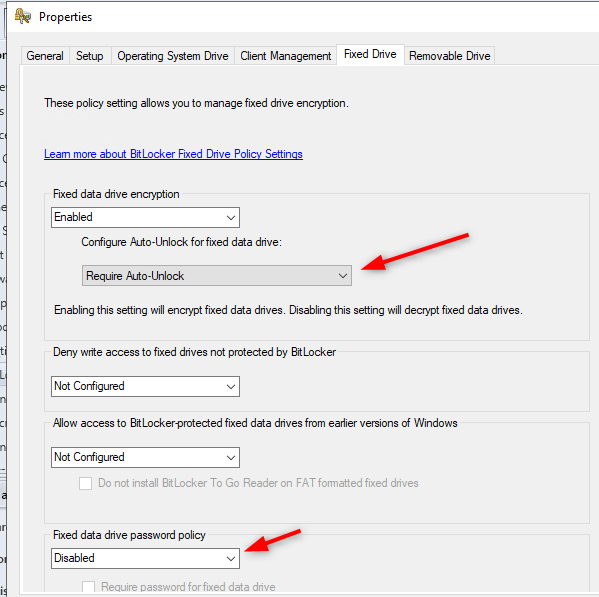
- Configure the Auto-Unlock for fixed data drive: Require Auto-Unlock OR
- Configure Fixed data drive password policy: Disabled
If you configure both the settings, you are still good to go but either one of them is mandatory to suppress the Bitlocker UI and do silent Bitlocker encryption.
After the changes are made and the client receives the updated policy, it started the fixed drive encryption silently and escrows the keys to the site server.
Hope it helps!
Recommended reading:















Only authorized users can leave comments
Log In