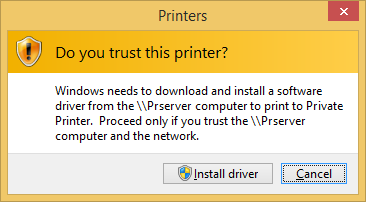
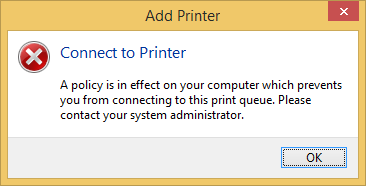
We came across a strange issue today on Windows 10 devices that we haven’t seen since the Windows Vista days. Users have started to get prompts for User Account Control(UAC) when connecting to some printers. The Point and Print feature is responsible for this as it easily allows standard users to install printer drivers from the trusted print server. This post describes how to fix Windows 10 point print UAC problem.
The problem appeared right after applying last July monthly updates. (MS16-087)
[su_box title=”Description” style=”glass” title_color=”#F0F0F0″]This security update resolves vulnerabilities in Microsoft Windows. The more severe of the vulnerabilities could allow remote code execution if an attacker is able to execute a man-in-the-middle (MiTM) attack on a workstation or print server, or set up a rogue print server on a target network.[/su_box]
Windows 10 Point Print UAC Prompt Cause
Microsoft as tightened the requirement for printer drivers on print servers.
If you :
- Are using a print server
- Allow standard user to install printer drivers using the Point and Print Group Policy
- Are using old printer driver that might have the following :
- Non-package-aware v3 printer drivers
- Unsigned or expired certificate validation drivers
Following MS16-087 installation, you receive a UAC prompt and a Connect to Printer error after a printer installation attempt. (A policy is in effect on your computer which prevents you from connecting to this print queue. Please contact your system Administrator)
Here’s the list of the specific KB per OS that create the issue :
- KB3163912
- Windows 10
- KB3172985
- Windows 10 v1511
- KB3170455
- Windows Vista
- Windows 7
- Windows 8.1
- Windows Server 2008
- Windows Server 2008 R2
- Windows Server 2012
- Windows Server 2012 R2
How to fix Windows 10 point print UAC
Part 1
Part 1 of the solution is available in the October 2016 Preview of Monthly Quality Rollup available for all operating system except Windows 10 (October 16th). Microsoft has released an update that lets network administrators configure policies that permit the installation of print drivers that they consider are safe. This update also allows network administrators to deploy printer connections that they consider safe.
[su_box title=”Note” style=”glass” title_color=”#F0F0F0″]If you are not familiar with preview updates, take a look at the following blog post.[/su_box]
This mean, if you are facing the issue, the official fix for it will be available for production use on the next Patch Tuesday (November 8th) as part of the Monthly Quality Rollup.
[su_box title=”Important” style=”glass” box_color=”#000000″ title_color=”#F0F0F0″]**Update 2016/11/10** Microsoft as released an update that was in preview in Octobre 2016. KB3197868 https://support.microsoft.com/en-ca/kb/3197868 After testing, it’s working as excepted. The second GPO part still required to make this work.[/su_box]
KB in preview
For Windows 7 and Windows Server 2008 R2 : https://support.microsoft.com/en-ca/kb/3192403
For Windows Server 2012 : https://support.microsoft.com/en-ca/kb/3192406
For Windows 8.1 and Windows Server 2012 R2 : https://support.microsoft.com/en-ca/kb/3192404
KB in production
For Windows 10 RTM : https://support.microsoft.com/en-ca/kb/3192440
For Windows 10 1511 : https://support.microsoft.com/en-ca/kb/3192441
Part 2
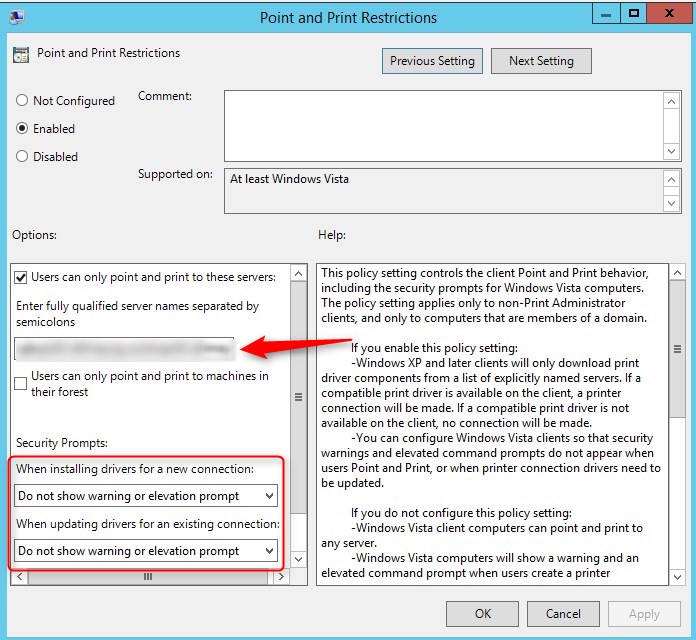
Part 2 consist having the right GPO settings for Point and Print.
Two GPO settings must be applied :
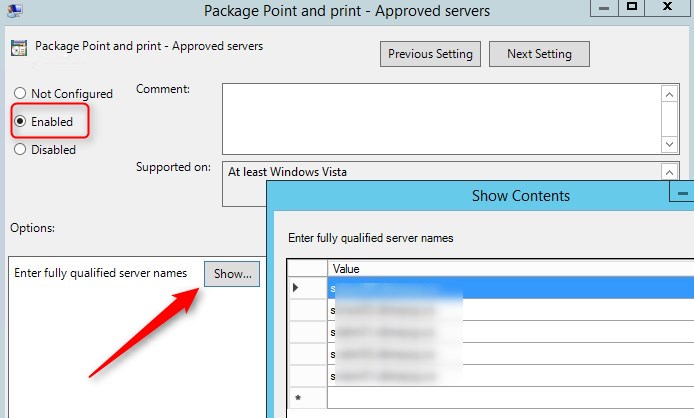
- Under Computer Configuration / Policies / Administrative Templates / Printers, set Package Point and Print – Approved server to Enabled
- Each print server must be added to the list with the fully qualified server name
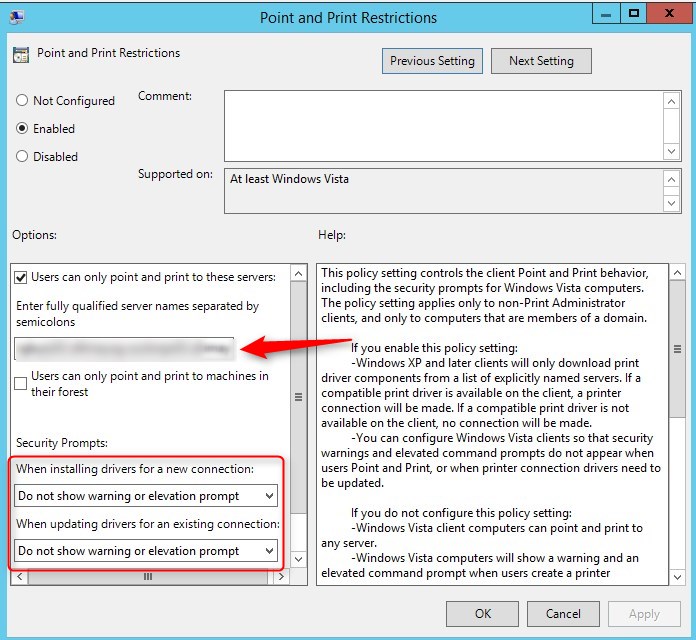
- Under Computer Configuration / Policies / Administrative Templates / Printers, set Point and Print Restrictions to Enabled
- Each print server must be added to the list with the fully qualified server name, seperated by semi-colons
- When installing driver for new connection, select Do not show warning or elevation prompt
- When installing driver for existing connection, select Do not show warning or elevation prompt















Connect Epson WF-3725 Printer to wifi
04.17.2020 AT 10:27 PMJohnson
07.24.2019 AT 01:10 AMNomi
05.29.2019 AT 03:39 PMjenny
05.17.2019 AT 05:37 AMcdhpl.com
05.15.2019 AT 06:18 AMJeff G
10.31.2017 AT 01:44 PMEddy
02.14.2018 AT 12:03 PMRaphus
04.13.2017 AT 06:27 AMJeff Scharfenberg
11.07.2016 AT 11:31 AM